Your phone is one of the most personal items you own. It carries your thoughts, your search history, and worse — your bank details. Bad dreams about your phone getting hacked are enough to cause cold sweats. When it happens in real life, it can turn your whole life upside down.
According to statistics reported by RSA Security, 80% of attacks against phones come through apps. Worrying, right? I mean, how often do you think twice before downloading? This article covers what you need to know to keep your phone safe from spyware. I’ll also cover how to know if someone is spying on your phone and what to do if they are.
We’re here to clear the air on all things spyware-related. Here’s our list of 9 tell-tale signs someone is spying on you.
Are you worried about your phone’s security? Add an extra wall of protection by encrypting your internet traffic with a VPN. Get CyberGhost VPN to prevent people from spying on your phone through your online connection. It also masks your IP address to throw snoopers off your scent.
How Do Phones Get Infected With Spyware?
Spyware allows perpetrators to covertly obtain private data from your phone. Just like any type of malware, you can get a spyware infection on your devices in multiple ways.
It’s important to keep your phone security under control to reduce the number of cybersecurity vulnerabilities you’re exposed to. Let’s take a closer look at how spyware can end up on your phone.
1. Malicious Apps
Not all apps in the App Store or Google Play Store are genuine and harmless. The sad truth is popular app stores host many harmful and fake apps. It’s all too easy to download a malicious app out of curiosity or by mistake. To avoid getting a nasty spyware infection, you should know how to spot fake apps.
2. Poor Phone Security
Suboptimal phone security makes you more likely to end up with a spyware infection.
Most popular phone brands patch security vulnerabilities on an ongoing basis. When new updates are available for your device, install them as soon as possible. For an extra layer of security, get a reliable anti-malware app and scan your phone regularly.
3. Phishing Emails
One of the most common ways of getting malware infections is through phishing emails and messages. In general, you should always avoid opening emails from unfamiliar senders. Whatever you do, don’t open random links sent by email.
It’s not always easy to spot phishing emails or SMS phishing — but sometimes, they’re obvious. For example, you might receive an email saying you’ve won something, and all you need to do is click on the link. Don’t do it.
4. Wi-Fi Attacks
Malicious hackers and snoopers often lurk on public Wi-Fi networks to catch unsuspecting victims. This is because open networks have poor security and it’s easy to infect devices across a shared network. Keep yourself safe on public Wi-Fi by using a reliable VPN to keep your device’s connection activity hidden from snoopers.
CyberGhost VPN protects you from Wi-Fi attacks by redirecting your traffic through a private server. Get CyberGhost VPN to enjoy an ultra-safe browsing experience when you connect to open Wi-Fi.
5. Direct Installation
It’s less common to get malware infections through direct installation. A person would need physical access to your phone and have time to install it manually. You can easily avoid this by not leaving your phone unlocked or lying around — keep a close watch on it!
How to Check for Installed Spyware on Phones
Here’s how you can check if someone tampered with your phone settings.
For Android Phones
- Go to Settings
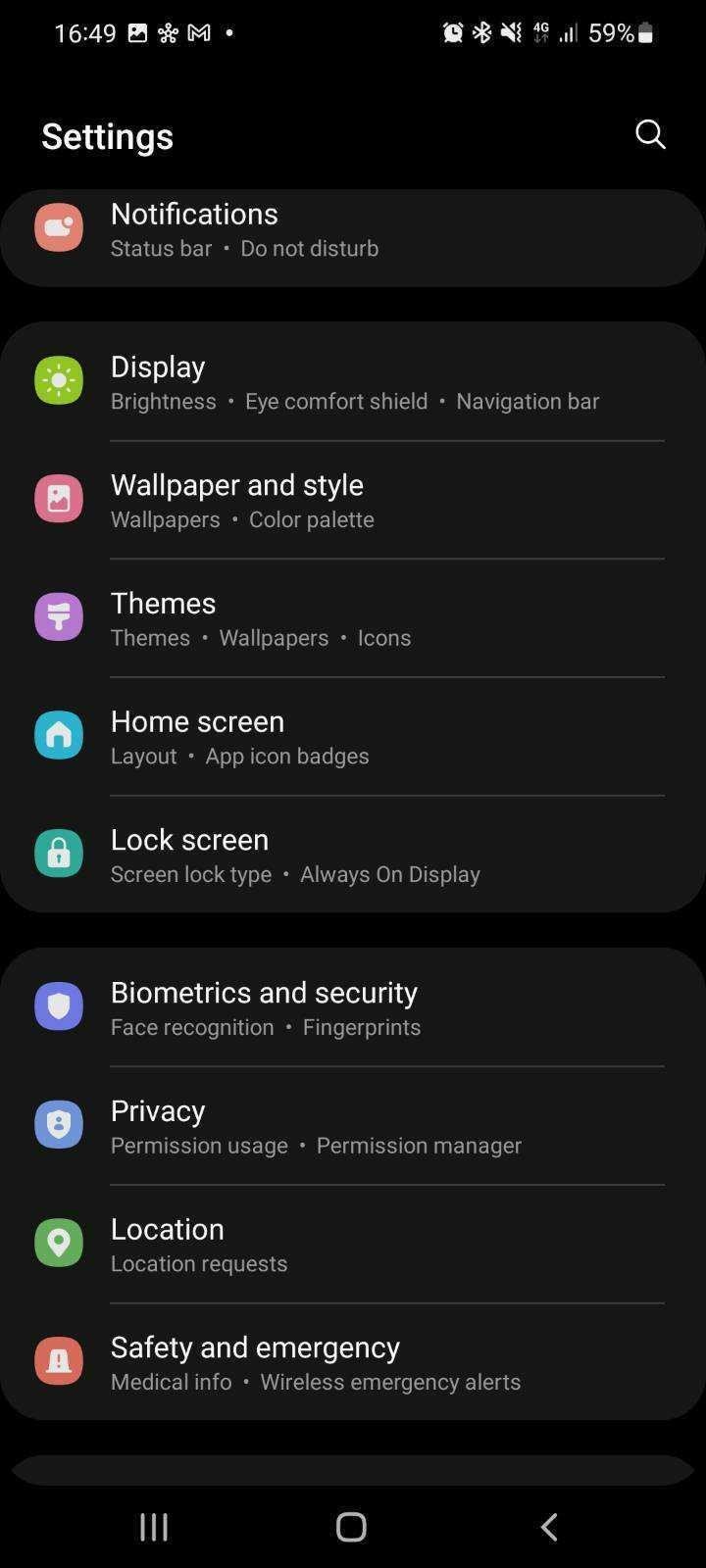
- Tap on Biometrics and security
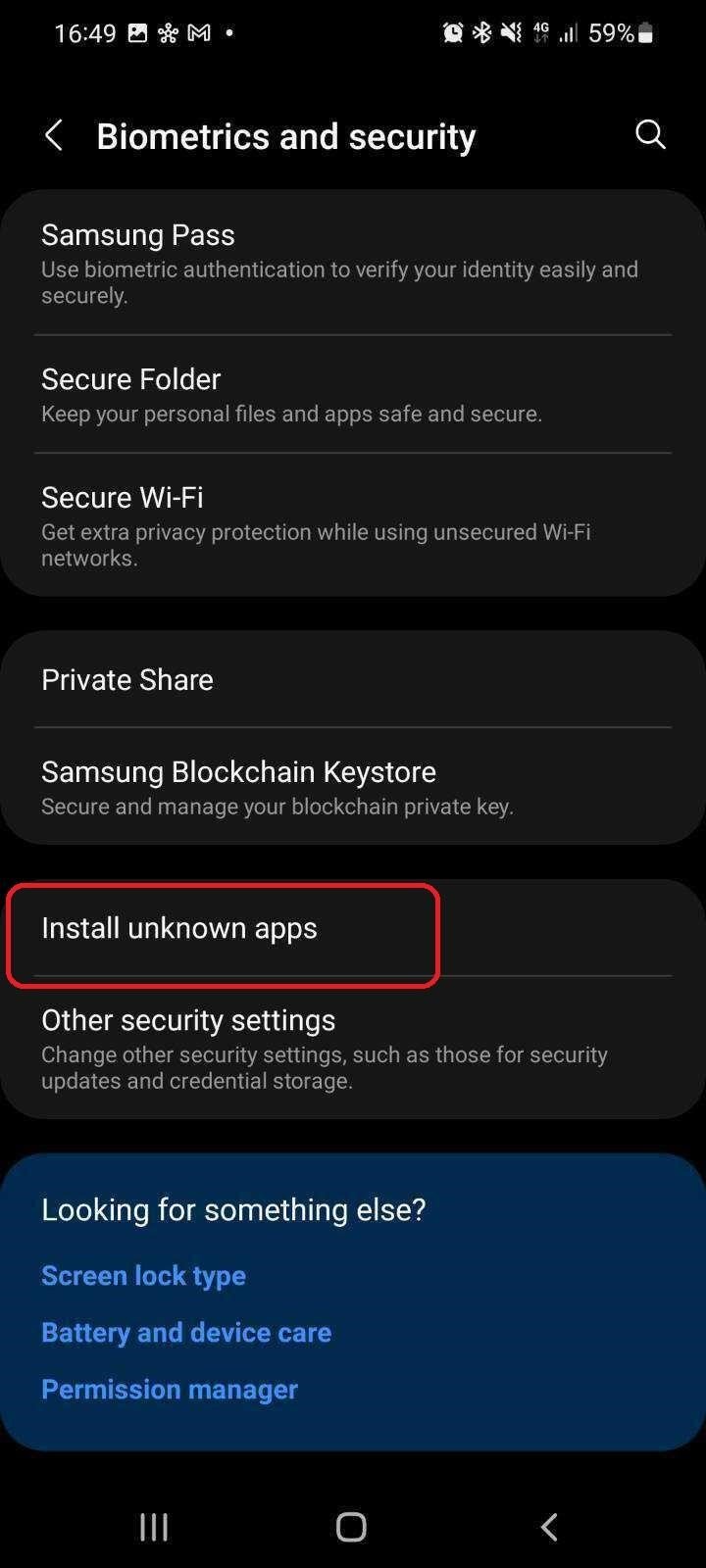
- Tap Install unknown apps
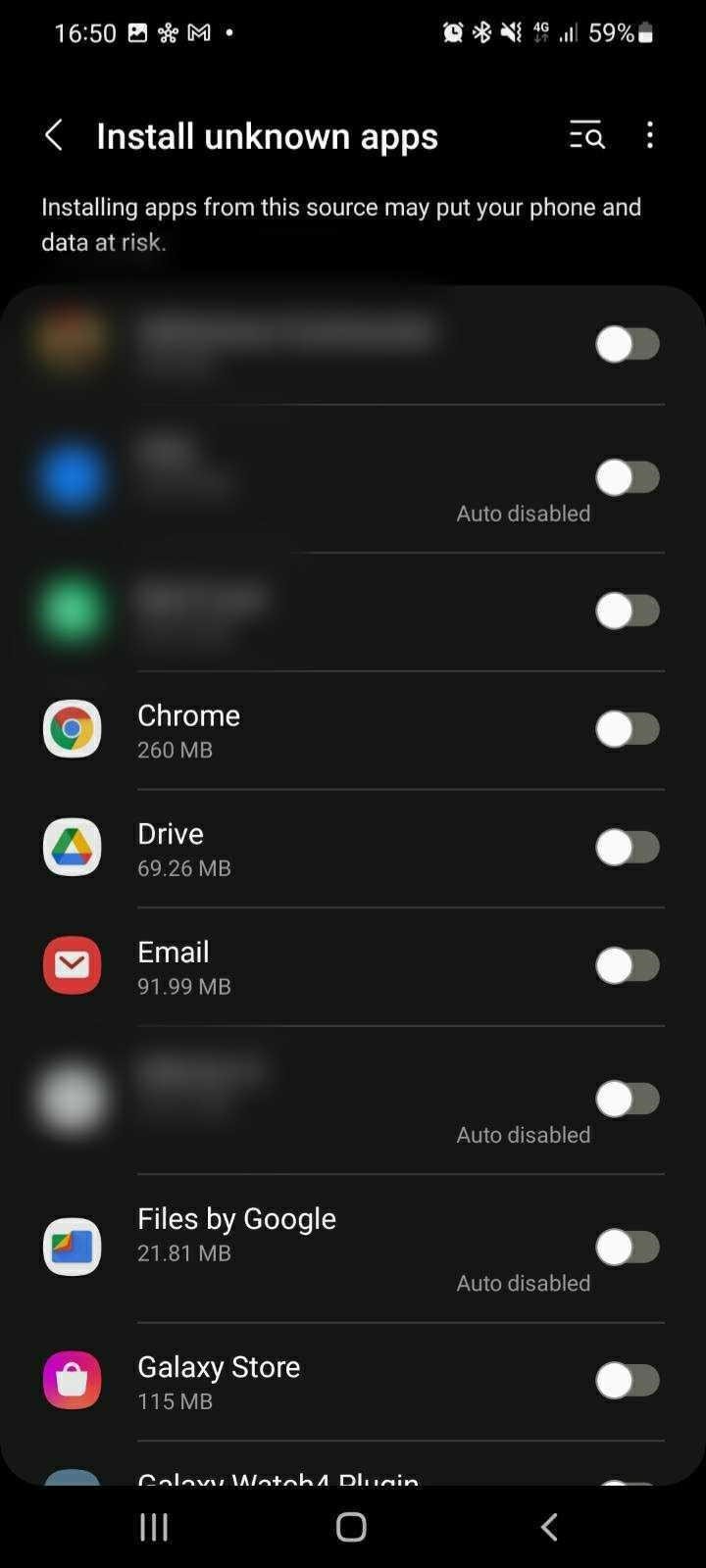
- Check if any toggle switch button is enabled
On iPhones

Apple’s security is pretty tight, so you’re far less likely to get a spyware infection if you roll with an iPhone. That said, it’s not impossible for it to happen either. Keeping your phone updated and steering clear of suspicious links and apps should cover you.
Note: Jailbreaking your iPhone weakens your device security. You won’t have Apple’s virtual henchmen to protect your device and your phone will be more vulnerable to attacks.
How to Recognize Spyware Apps
Hopefully, you’ll never have to ask yourself “Is my phone being tracked?” because it’s a stressful thought. You can avoid getting to that point by learning how to recognize spyware before you press install. It also helps to know what to do if you think your phone is infected.
Spyware apps won’t always be labeled as spyware, even though you might have come across a few. More often, they’ll be disguised as something else that looks genuine. The best way to find out whether an app is the real deal is to check reviews and online forums. Here’s a list of common spyware apps — delete them if you see them.
| Spyware App Name | Available for Android | Available for iOS |
| mSpy | ✔️ | ✔️ |
| FlexiSpy | ✔️ | ✔️ |
| PhoneSpector | ✔️ | ✔️ |
| Cocospy | ✔️ | ✔️ |
| Spyic | ✔️ | ✔️ |
| MobileTracker | ✔️ | |
| Android Spy | ✔️ | |
| MobiStealth | ✔️ | ✔️ |
| Spyera | ✔️ | ✔️ |
| SpyBubble | ✔️ | ✔️ |
| FoneMonitor | ✔️ | ✔️ |
| OpinionSpy | ✔️ |
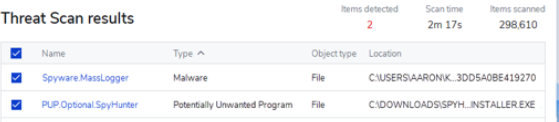
If you suspect you might have spyware on your phone, download an anti-malware app and run a virus scan. If any Potential Unwanted Programs (PUPs) show up, delete them.
Pro tip: Spyware won’t always come up in a scan. If the malware is well-hidden, you’ll need to find other ways to weed it out. If all else fails, reseting your phone to factory settings could be the only way to wipe the spyware for good — but make sure to back up any important files and data first!
It’s also helpful to recognize any weird phone behavior. It might indicate it’s infected with spyware. Here are 9 signs you should look out for.
Is My Phone Being Tracked? 9 Signs You’ve Got Spyware
Unlike Trojans or ransomware, spyware doesn’t cause direct damage to your system. It’s not in your face like other malware. Spyware tends to work quietly behind the scenes, recording your every move. Worried you might have spyware? Here are a few signs someone could be spying on your phone.
1. You Use Too Much Data
Most of us will rarely have high spikes in data usage unless we travel or face an emergency. You can generally gauge how much data you use based on your online activity. Here are some examples for reference:
-
- ⌚ HD streaming takes about 900MB/hour.
- ⌚ Video conferencing, like Zoom or FaceTime, takes about 480MB/hour.
- ⌚ Online gaming takes about 60MB/hour.
- ⌚ Streaming music takes about 30MB/hour.

Spyware tools eat up a lot of data because they rely on a constant active connection. They need one to send collected information from your phone.
2. Rapid Battery Drainage
If you’ve been unlucky enough to get a spyware infection, your battery will start acting up. After charging it all night, you might look at it at 2 p.m. to find it’s nearly dead. If this happens, you might want to investigate the cause.
It’s worth noting that malware isn’t the only thing that can drain your battery quickly. Batteries degrade over time, so don’t panic just yet. However, if you notice this sign alongside several others, it’s time to take action.
3. Phone Overheats
Running spyware consumes significant processing power, which increases CPU usage. As a result, your phone’s processor works overtime to fulfill power demands. The high workload causes heat, and if your phone’s ventilation system can’t handle it, your phone will be hot to the touch.
If your phone overheats and you’re not busy with heavy-duty activities like gaming or have a lot of apps open at the same time, it might be time to ask yourself “Is my phone being tracked?”
4. You Hear Weird Sounds During Calls
Notice odd clicking sounds? An airy drift? Static noise?
Unless you’re in an area with poor coverage, it’s a sign someone is eavesdropping. Spyware is a likely culprit. It can record your phone calls and produce weird background noise in the process.
In some cases, you’ll also notice these weird sounds during video conference calls like FaceTime or Zoom. If this issue persists and isn’t tied to a specific app, you’re possibly dealing with a spyware infection.
5. Your Phone Feels Sluggish
Most smartphones last from 3 to 5 years. When the hardware gets outdated, you’ll start to notice apps taking longer to load, taps taking longer to respond, and websites taking longer to open. That’s normal.
Spyware takes it to the next level. You could have a brand-new phone, and it will be slow to respond to basic functions. This is because spyware takes up a lot of resources. It overloads your phone’s memory, battery, and CPU, so your phone will feel sluggish to the point of frustration.
6. You Notice Suspicious Changes and Charges
Don’t remember installing that funny-looking app? Can’t find an explanation for the latest Google Play charges?
Some spyware offers the perpetrator remote control of your phone. That means they can access and make various changes to your device. They can add or delete apps, make unauthorized payments, and even mess up your settings.
If you’re dealing with this spyware type, it can compromise your financial details. You should quickly take measures to protect your accounts.
7. Signs of Activity in Stand-By Mode
Some forms of spyware let hackers control your phone remotely. While they typically try to do this without you noticing, you might catch signs of it. Here are some things to watch out for on your phone:
-
- 🚧 Screen lights up for no reason
- 🚧 Camera opening for no apparent reason
- 🚧 Phone sending messages by itself
- 🚧 New bookmarks in your browser
- 🚧 Browsing history full of unfamiliar activity
- 🚧 Stores private information in your screenshot gallery
8. Slow Shut Down & Start Up
Still wondering how to know if someone is spying on your phone? Slow shut down and start up times are a major red flag. Whenever you shut down a device, the operating system closes background apps to prevent them from crashing. Naturally, the more apps you have running, the longer shut down takes.
Since spyware runs programs in the background, it uses a lot of power. It also pushes to use more resources and resists shutting down. For these reasons, you’ll notice a considerable lag when you try to shut down your phone.
The same logic applies to when you start up your phone — spyware programs will delay it.
Avoid getting caught in a spy’s trap by using military-grade VPN encryption to protect your data. CyberGhost VPN offers you an ultra-private browsing experience so you can avoid spyware attacks, even over free Wi-Fi. Get CyberGhost VPN to help protect your phone from spyware.
9. Your Notice Strange Credit Card Activity
The number one target for spyware is your financial credentials. Cybercriminals target you through your banking app or any payment platform with a linked credit card.
Cybercriminals rarely use spyware just to troll you. They mainly use it to steal financial information and impersonate you. You might notice small suspicious charges first. After all, no one panics for a $3 charge.
After a while, they’ll get their hands on your IBAN, credit card number, CCV, SWIFT, and whatever else helps them transfer funds. If you notice any suspicious activity, contact your issuing bank immediately. They’ll advise you further.
How to Remove Spyware from Your Phone
You’ve read the tips on how to know if someone is spying on your phone, what’s next? If you suspect a spyware infection, you should take steps to remove it immediately. Luckily, removing spyware and saving your phone is still possible. While some spyware can be stubborn, following these steps should help you.
1. Run a Malware Scan
Since spyware is a type of malware, running a malware or anti-virus scan can help you remove it. Bear in mind — more sophisticated spyware is hard to detect. For this reason, doing multiple scans with different programs can be beneficial. It’s also worth getting a paid anti-malware program to give your phone the best chance.
2. Change Your Passwords

Whenever you have reasons to believe spyware is compromising your privacy, change your passwords immediately from another device. Otherwise, cybercriminals can just get your new passwords through spyware. Choose strong and secure passwords and consider adding some extra protection, like two-factor authentication.
3. Enable Two-Factor Authentication (2FA)
2FA strengthens your accounts’ access security. Besides your password, 2FA requires you to validate your identity through another method. Most commonly, it’s a code sent via text message or email.
2FA codes change with every login and are available for a short period. That makes them more secure than a single password especially when most people never change their passwords. Securing your account with 2FA also prevents cybercriminals from accessing your accounts when they already have your passwords.
4. Update Your Operating System and Apps
Like a lot of malware variants, spyware relies on outdated and ineffective security measures to infect your device. That’s why you should regularly update apps and operating systems. Updates come with crucial security patches to hinder malware from exploiting vulnerabilities. For example, an up-to-date antivirus recognizes the latest cyberthreats and an up-to-date system can prevent spyware from working properly.
5. Reset Your Phone to Factory Settings
If you find yourself dealing with a particularly resilient spyware, your last resort is resetting your phone to factory settings. That process wipes all your files, accounts, and information from your device. More importantly, it’ll wipe out all spyware programs.
Normally, I’d recommend having a backup before a full factory reset, but you could back up spyware remnants by mistake. Weigh your options carefully before you decide a factory reset is the best option for you.
How to Protect Your Phone from Spyware
Defense is the best offense! Spyware is a stealthy threat. It takes a long time for people to realize they have a little spy on their phone. That’s why you should learn how to protect your phone from spyware.
🔒 Don’t Leave Your Phone Unattended
It’s easier for someone to install malware on your device if they have direct access to it. Always be mindful of where you leave your phone and who can access it.
🔒 Lock Your Phone
A phone lock is a great security measure to have. PIN codes, face unlocks, and fingerprints make it harder for anyone to use your phone without your consent. Biometric logins are harder to break than a 4-digit code, so make good use of them.
🔒 Use CyberGhost VPN
CyberGhost VPN redirects your traffic through a remote tunnel to keep trackers and snoopers off your back. It also encrypts your data so if cybercriminals intercept your traffic, they won’t be able to make any sense of it. CyberGhost VPN also redirects your traffic through HTTPS sites to encrypt your connection.
🔒 HideYour Files
Spyware scans your files and folders and can even access your private photos and videos. Use CyberGhost Photo Vault to hide your media behind an encryption layer.
🔒 Avoid Apps from Unverified Sources
App developers need to abide by both the Play Store and the App Store’s terms, conditions, and security standards. Apps also clearly need to specify what permissions they require. Although it’s not a perfect system, stores take down apps in violation of these terms. Third-party websites can have apk files, but no one can verify these aren’t laced with malware.
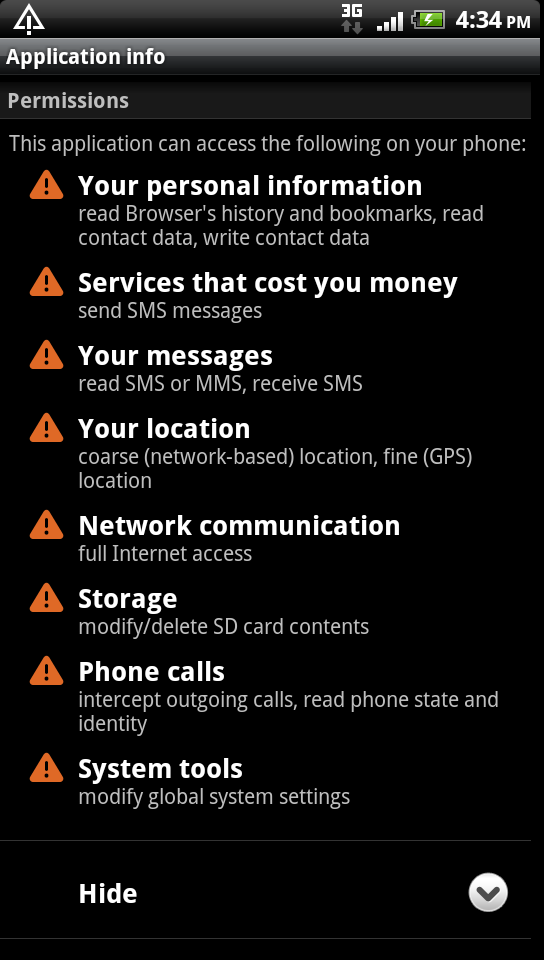
🔒 Check Every App’s Permissions
Whenever you install a new app, it may ask you to approve different permissions. An online game will require internet access, while a photo editing app will need access to your gallery. Any suspicious permissions are a red flag. Pay attention to apps asking for camera, microphone, messages, or NFC access. These can compromise your privacy.
Spyware Is Here to Stay

The unfortunate truth is spyware isn’t going anywhere soon. Despite the damage it causes to people’s lives, it’s a difficult thing to pin down and defeat. While cybercriminals commonly use it for ill-gotten financial gain, spyware is also used in a myriad of other ways.
-
- 🚩 Parents use it to keep tabs on their children
- 🚩 Jealous spouses use it to monitor partners
- 🚩 Governments use it for espionage
- 🚩 Dictators use it to track dissidents and journalists
- 🚩 Intelligence agencies use it for citizen surveillance
Covertly installing spyware on another person’s device is illegal in most countries. Unfortunately, that doesn’t make it any less common or problematic.
Defend Yourself Against Spyware
Spyware affects people all over the world. Whether it’s someone you know or an outside entity spying on your phone, it can lead to serious problems. Your personal information could leak into the wrong hands, someone can try blackmailing you, or hackers can steal from your financial accounts.
If you’re here to find out how to know if someone if spying on your phone, hopefully, our tips were helpful. Irregular activity on your phone like the examples I mention above may be tell-tale signs your phone is infected with spyware. Follow the steps I outlined to remove it from your phone.
Despite spyware being a well-known problem globally, the war against it is far from over. The best way to defend yourself is to know what to look for and how to deal with it.
FAQ
If someone is using spyware to spy on your phone, you might notice the following changes to your phone.
1. Mysterious data-use increases
2. Rapid battery drainage
3. Phone overheats
4. Strange noises during calls
5. Phone gets sluggish
6. Suspicious changes and charges
7. Signs of activity in stand-by mode
8. Slow shut down & start up
9. Unfamiliar credit card activity
Spyware usually runs quietly in the background, so it can be hard to detect. However, if you’re experiencing one or more of these signs, it might be time to take action. Think you might have spyware? Here’s how to remove it.
No single app can definitively tell you if someone is spying on you. However, anti-malware and anti-spyware apps might be able to detect spyware on your phone. If the anti-malware system is familiar with the type of spyware installed, it can detect it. More sophisticated forms of spyware are more difficult to detect. For this reason, it can be helpful to run scans with a few different anti-malware programs.
Worried your internet activity is being watched? Get CyberGhost VPN to enhance your digital privacy. Our military-grade encryption gives you an ultra-private browsing experience.
While you won’t always be able to tell with certainty, some red flags and indicators can give you a fair idea. If your camera light comes on randomly and if you notice photos or videos saved that you didn’t take, someone could be watching you.
Other signs include battery drainage, mysterious background app activity, messages or emails you didn’t send, and unexpected screen behavior. If you’re experiencing some of these signs, take action to remove spyware, secure your financial accounts, and change your passwords.
Pro tip: Use a different device to change your passwords and connect to a VPN for extra security.
Yes, most spyware is designed to run incognito without attracting attention. For this reason, it’s not always easy to know if you’re being spied on. To find out more, read my guide on how to know if someone is spying on your phone.
Yes, VPNs are a great anti-spying tool to have in your anti-surveillance toolkit. They protect your data from snoopers over your Wi-Fi network, cybercriminals, tracking, and ruthless advertising. While it’s not the only digital privacy tool you should be using, it’s important to always use a VPN.



Leave a comment
Angel Boehm
Posted on 11/03/2023 at 11:11
Hi there. I found this info very helpful. I am currently dealing with cybersecurity attacks. I believe it is my ex and his girlfriend. The both work for Microsoft. He is an Engineer and UI Designer. He also works on a team that handles site securities for the government , which makes him highly technicaly capable. He has access to my computer through a thunderbolt connection we had when we lived together. I have taken ALL the suggestions and steps from your site and been working with Apple. At this point they have told me to get a Forensic Computer tech. I have already contacted law enforcement, but the type of evidence they need is hard to grab when you are dealing with someone who is covert. It’s super scary. Until I can turn my devices over to a Forensics specialis, I just have to live with these two all up in my devices, my life etc. it’s so lame
Ghostie
Posted on 14/03/2023 at 11:10
We’re so sorry to hear you’re going through this, Angel. Hopefully you get the evidence you need soon. Stay strong!
Ariana Awer
Posted on 16/02/2023 at 19:38
Hi recently I believe someone has infected all my kids phones and my phones with malware as well as my smart tvs! I know it’s my boyfriends sister this girl has a really sad obsession with me and has finally found a new friend just like her so they have been teaming up! Saddest part is she doesn’t really show that she cares about my boyfriend they just like to control him… she’s older than me but behaves like a 12yo.. all of this for nothing… all I ever did was stick up for her and tell him to help her.. but honestly she’s trashy.. way too old to be playing these childish games… now my man actually has a family that cares about him and helps him… how do I remove all this malware… I noticed a while ago I was getting all these text messages with links abcs now they are talking through the mics on my phones and TVs I’m not going anywhere! If she want so childish I would’ve gladly left.. the condition of this building is nothing to fight for SMH! I’m always dumping my money into something (pest control) we had drain flies pantry moths mice galore spiders galore… red and black ant problems… roach problems centipede problems mold problems.. cracks in the walls… as well as so many other issues and bugs I’ve never seen.. I could easily call the board of health.. they condemn this place… No way they have the money to put into this dump.. even had my own place furnished and paid for an entire year but I have a soft spot for my bf so we stick together through all the traps this woman has laid but lately it’s getting too childish… haven’t played these games since middle/high school
Ghostie
Posted on 20/02/2023 at 11:27
We’re sorry to hear you’re going through this, Ariana. Have you tried following the steps we provided under How to Remove Spyware from Your Phone? You might also want to check out our steps for removing router malware and fileless malware. If you’re still unsure what to do, we’d recommend checking out a local shop for hardware repair or technical support like iCare for Apple products.
Winn
Posted on 08/02/2023 at 13:56
Very useful information that you have given on spyware, thank you very much. God bless you. But how can I know that Ghost VPN itself is not a hidden spyware?
Ghostie
Posted on 09/02/2023 at 10:29
Hi Winn. Glad to hear you found the article useful.
CyberGhost VPN operates under a strict No Logs policy and our apps were developed under the Privacy-by-Design principles. This means our service was designed to prevent any data storage. We don’t track or store what you do online while you are connected to our servers.
Our systems have also been independently audited. Professionals from Deloitte inspected our servers and systems, and concluded they are in line with our policies. You can read more about it here.
Nathaniel Ejeta
Posted on 26/12/2022 at 14:12
have learnt a lot and I have also gained enough knowledge from this content.
Ghostie
Posted on 27/12/2022 at 17:55
Good to hear Nathaniel. Thanks for reading our blog.
Pam Wallis
Posted on 01/02/2023 at 19:35
I had to get rid of my apple phone. I am a 64 year old Wan and stone has taken over my life with suff they put on the social media sites pretenti g to be me, and this is my Hisbands phone John and I believe it is on this phone as well. My life has been ruined,I don’t do social media,and don’t have wifi either, my family have a banded me, and I have no friends anymore as well. Please help
Ghostie
Posted on 02/02/2023 at 10:37
Hi Pam. Unfortunately, your message doesn’t contain that many details for us to offer any additional advice. Have you considered checking your husband’s phone at an iCare center for malware or viruses?
David
Posted on 03/12/2022 at 14:34
I’m a technological dinosaur.
Thanks for interesting reading.
All my keys on phone moved on Thier own for a while like someone was controlling my phone. Unless it was water in it ?
When I call my Dad
It says call waiting until it’answers band it says call forwarding. My.mate says my calls to him are traced and more nitored.
If I’ve alr at got some spyware on my phone and am being traced tracked and monitored.
Do I have to buy a new phone, get a new SIM card. Or both.
And if I put Ghost vpn or protectstar.on phone. Does this kick out any spyware on phone that is there. Or just.protect for future attack.
Sorry for all questions , but this is new to me and scary.
If someone has my number and I get a new number from my.provider. can someone find out my new number on a computer from having my old number. ?
One last question. A page came up on my phone that I’ve never seen before.
Saying that UI was installed. Is this a problem. Actually. This is my last Q . Promise. Can a download be sent to phone that can harm someone physically ? Can the phone be used as a weapon to harm the person or cook them from the inside out. ?
It’s a serious question.
Thankyou
Ghostie
Posted on 05/12/2022 at 14:40
Hi David.
It doesn’t really sound like a spyware problem but it could be another strain of malware. Have you checked the weird noises and call forwarding with your phone carrier? It might be something on their side.
CyberGhost VPN boosts your online security and encrypts your internet traffic. This helps keep snoopers at bay but it can’t delete spyware on your phone. Before switching your phone number, you could try installing an antimalware app or resetting your phone to its factory settings.
It’s perhaps best to contact a local phone repair shop, and have them take a look.
Stay safe!
Daniel
Posted on 23/08/2022 at 01:22
Your the best of the best! THANK YOU!!!
Ghostie
Posted on 24/08/2022 at 10:51
Thank you for your kind words, Daniel. Glad to hear you enjoyed reading.
spy
Posted on 29/01/2022 at 13:31
Very useful content, thank you for sharing this.
Adina Ailoaiei
Posted on 31/01/2022 at 09:17
Glad to hear you enjoyed reading, Ghostie. 🙂
William Perkins
Posted on 28/01/2022 at 08:24
So I know there is spyware on my phone from my soon to be ex wife. She knows when I change my passwords, she logs into my Google accounts I have all the stomach. And she told me she is watching me. But I can’t find the app to get it off. I’ve done a factory reset 9 times on both phones and I have enable 2 authentication, I’ve checked apps and the one that is on the most is Google there is a small foot print in my activity “Google” what do I do now. I’ve down loaded malware and spyware apps. But she is still on there. Can you help?
Adina Ailoaiei
Posted on 28/01/2022 at 11:18
Hi William. Sorry to hear you’re going through this. It’s hard to say based on the information you provided. In this case, it’s better to contact a professional service or get in touch with local authorities. They can further advise on the matter.
Kathleen ricks
Posted on 09/07/2020 at 18:54
I think all phones should come with a VPN spy app malware removal tool app instead of those stupid games and APS we don’t even want
Adina Ailoaiei
Posted on 14/07/2020 at 12:30
That would indeed be absolutely great, Kathleen. We can only dream.
Amber
Posted on 09/05/2023 at 18:39
Absolutely!! Agree with you 💯% 👍🏻
David
Posted on 02/07/2020 at 00:36
Can you shed some light on some that’s happening on my new kindle hd .When on outlook and some Google apps when I open outlook and open in box message and I click on a link on the email of some sites it opens and then shuts imedently and I end up back at the email I open so I can’t see the like as it will not open .
Thanks
Adina Ailoaiei
Posted on 14/07/2020 at 16:18
Hi, David! Don’t worry, that doesn’t really sound like a spyware problem. Some Kindle users have reported issues opening Outlook in landscape mode since the latest update. As far as I’m aware there’s no patch planned on Microsoft’s side as of yet. If you still have concerns, you can check out more info on Microsoft’s Help pages.