We talked with Graeme Speak, Founder/US Operations Manager at BankVault.com about how Password Managers are not secure, what ideas Graeme and his team bring to the table and how can we protect ourselves from all the cyberthreats.

I’m curious about cybersecurity. The first question is about passwordless authentication: what motivated your search for that solution? What are the strongest points of that idea?
I realized that Password Managers are not secure. When they load your encrypted password into a webform the password is no longer encrypted. It is clear text and intercepted instantly by any malware (Man-in-the-Browser). There is nothing Password Managers can do to fix this this because its a fundamental issue with the way browsers work. I had an idea that had been running around my mind for the last 4 years about creating a new type of password manager. At the last RSA conference I engineered my way into a side event and met the head of security of one of the largest Password Management companies and pitched my idea. I described the problem that they can’t solve – how to stop a Man-in-the-Browser. I said, “You can’t solve this problem but I can”. He looked at me and said, “So how do you do that”. That instantly validated everything I had been thinking. They can never solve their issue because their entire footprint exists on the users device. There is a single attack surface. Until now, the industry has been pushing 2 Factor Authentication. My idea, which was based on our previous innovations, was a way that would harness the webserver and step this up over time, creating a new type of protocol. I didn’t tell him the answer, but walked out and rang my team. We started to build a Password Manager that would have a formidable technological advantage. In the R&D process we realized that this would enable any website on the plant to offer their users a Passwordless option. That market is about 40x larger the Password Management industry. So this is what wanted to build. And our approach is completely unique because it leverages earlier technologies we had built and patented.
In June, passwordless authentication became the highest funded sector in cybersecurity. Analysts predict 90% adoption, as the industry grows from 45 billion dollars this year to 456 billion dollars by 2030. This is a really big change that the industry will race to embrace over the next 12 months and beyond.
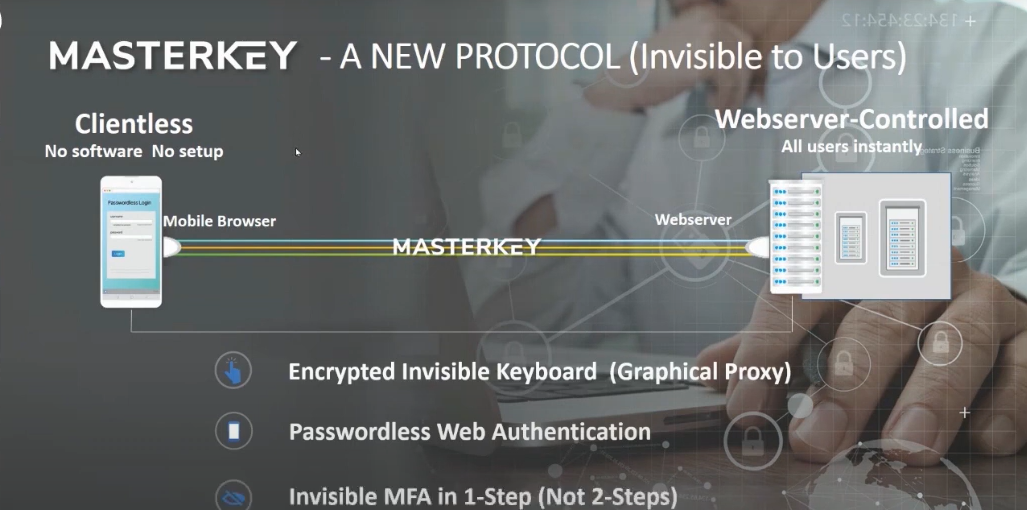
We’ve been pioneering this space since 2015. We have 6 patents filed worldwide, 5 products in the market, and we’ve just released a new technology called MasterKey, which allows any website to go passwordless overnight. This is 10 to 100 times faster than any other solution available today. An organization would want to provide passwordless options to their customers because providing frictionless access increases user engagement. It is also incredibly difficult to compromise, so this provides much stronger security to users.
This is a win + win situation for users. And for the online service, this actually becomes a differentiator and a business driver for the organization. An organization can deploy this without any technology risks, or security risks. If you can deploy it overnight, then frankly – it’s a no-brainer. Why wouldn’t you?
My team is very proud of what they’ve developed with MasterKey. There are plenty of passwordless technologies in the market. All of these solutions suffer from the same common roadblock – these require a major implementation project: there’s data migration at the backend, deployment of client software to the users, who must go through a process of setting it up, which requires guidance – also called change management. Change management on a big user base can be the largest cost of the project.
DFrom a business’s point of view, this is a huge commitment – and we’ve solved all of those problems with MasterKey. The genius is that we are harnessing the users’ mobile phones’ browser, so there’s no software to install or configure, it’s deployed from the very front face of an organization’s web server. So this is a cosmetic that requires no change to the backend systems. It simply provides the users with a more secure and passwordless experience, without change anything.
When you are on a workstation, where you normally see username and password fields, we’ll have a QR Code next to it. If you scan it with your phone camera, it simply transfers the login page back to your mobile, which authenticates you. There’s nothing installed in any device or any setup. There’s no technology risk because there is no single point of failure – users can still login normally be entering their username-password login on the original web form. And there’s no security risk because this is the user’s normal input but, now controlled by the organization webserver so users never enter it again.
The kernel of the technology is something we call an Encrypted Invisible Keyboard, which is an illusion created on the mobile phone’s screen. There is no keyboard, it’s just a photograph of keyboard. The webserver sets up encoded cells on the mobile phone’s screen that only it can interpret when working in conjunction with that phone. When you press the cell that sits above, say the letter “a”, we never generate that letter; instead the system will generate perhaps 48 characters and these can only be interpreted by the webserver that set it up a moment earlier.
On top of that, MasterKey can also capture Proof-of-Presence that the original user is their, for example by their biometric scan. We’re talking to the world’s largest bank at the moment, who have asked for a 4th Factor of Authentication – the GPS coordinates of the phone. We can do as well.
What advice can you provide to someone with an idea but unsure about what first steps to take, based on your experience in tech entrepreneurship?
I love mentoring inspired people to take action on things! But I only want to encourage people who I am convinced can afford the time, that have the support around them so that if they ultimately fail, then they still have the time/energy/attitude to pick themselves up and keep going with something else. We only learn is by making mistakes and taking these hard-learned lessons forward into the future. I don’t want to mentor or encourage people who can’t afford to take the risk. But there is an important paradox here: it’s when a person is almost out of options and painted into a corner, that they discover how to climb the walls. It takes total stubbornness to continue in the face of adversity and this is one of the essential ingredients that define an entrepreneur. Most fail, so it’s not for the faint-hearted.
With this process, we have failed a lot. To get to the point of having 25 innovations, I can tell you we’ve failed thousands of times! It’s really hard, however, this is what it takes to change the world. I’m so proud of what my team has done over a number of years.
The best advice I can give is: validate that the problem you address is a really strong clear pain point. If you are going to do something that is nice to have then people won’t pay and it will not be worth your time.
If your idea is good don’t keep it secret. This seems counter-intuitive but you can never do anything by yourself, and really capable people who might copy you are normally too busy to copy your idea. You ultimately need to engage with other people. and If you share your ideas then you get real-world feedback. You get practice at enrolling others. You may get a willing customer before your product is ready.
I’ll give you a personal example.
I was in Beijing with two friends and my colleagues could not get their emails through the Chinese firewall. I could access my email using a virtual computer. The penny dropped that I could sell this “as a service” to the Chinese people. My friends replied that I would not succeed because the Chinese people didn’t know they had a problem. There was no pain point and so they would not buy it. I didn’t believe them, so I went ahead and built it. They were absolutely right: although it was incredible technology these Chinese people didn’t have a problem and so would not buy it!
That technology was incredible. We could build a remote virtual machine in 2-seconds when Amazon was taking 40-minutes. The breakthrough for me came when I was desperate and open to any other ideas. We had a call from a real estate agent who was terrified because the government was telling them that their bank accounts and trust accounts were being hacked successfully.
I realized we could employ our technology to solve this problem. Our pitch reduced to half a sentence – “We stop your bank account being hacked” – the emotional impact of it makes it immediately relevant to everybody. That was how we pivoted from developing cloud computing technology into a cybersecurity technology innovator.
Finally, I don’t ever try to cast over the horizon. The vast majority of startups and people in Silicon Valley with big dreams do that and most never succeed. I focus on issues right at my foot where I can solve an immediate problem that gives me an instant return on investment. This fuels you to do it again and again and again, refining your work.
We’ve had a growing problem during the pandemic with cybersecurity, including many ransomware and phishing cases. To what do you attribute that trend?
Suddenly, the world was pushed to work from home, which exposed many weaknesses. Organizations had no choice but to keep operating and had no control over what users did at home, outside their networks. By volume, over 99% of cyberattacks target PCs and smartphones. The industry calls these endpoint devices and this is called Endpoint Hacking. Its the weakest part of any network and it represents a massive attack surface.
There are a lot of devices out there. You can’t get to the servers because they are behind a firewall but a PC or smartphone interface the internet directly. Every device on the planet is different, so there’s a lot of cracks and fissures between the different software components and versions of these devices and that’s what the cyberhacking industry exploits.
There’s a lot of social engineering leading people to click on things to get more information. The goal is identity theft. I’ve recently read an analyst report that said financial malware as 2.5 times more abundant than ransomware. It’s more insidious too because it doesn’t show itself when it’s harvesting login credentials to online services.
All browsers are designed to run JavaScript instantly and there is no telling of what the code will do until it executes. Once in your browser, it can remain. On average a Man-in-the-Browser is there for 10 months before the hacker stings their targes. It’s very easy to harvest the login credentials, for example, to your banking account. And Password Managers cannot solve this problem. The moment your password manager loads your encrypted password into a web form, and the asterisks appear on screen, it is not longer encrypted and instantly exposed to any malware.
Ransomware has evolved now beyond encrypting data. The goal has moved on to stealing your data and then holding you or your organization to ransom. You never get rid of them because they plant backdoors throughout your network to get back in later.
Regarding those problems, what is the solution for companies and for users?
The same solution suits both individuals and organizations. We created a technology called WebSafe, which isolates the user from any malware on their device. The technical term for this is Remote Isolation. You should start by assuming your machine is already compromised. How would you know? You won’t because non-malware (legitimate code doing the wrong thing) is undetectable. WebSafe is analogous to going down the street and buying a brand-new laptop, using it once, and then throwing it away.
WebSafe does this using the cloud. It is a simple web service you log into which builds a pristine new remote virtual machine within one 1-second. These machines are invisible from the internet and so we call them invisible BankVault.
The desktop appearing in your browser is a completely independent secure environment. You can use it to conduct any online transaction, such as banking, accessing your crypto-exchange, or opening potentially dangerous email attachments, with complete immunity.
A really clever addition is an Invisible Encrypted Keyboard. If you scan the QR code on the WebSafe desktop with your phone camera, it will turn your phone’s browser into a keyboard that you can use for entering passwords. The only place in the universe that can merge a username typed from your local keyboard with the password typed on the Invisible Keyboard, is the virtual machine that you created a few moments earlier, and this machine is invisible from the Internet.
It does not matter if you open a virus or a compromised file, because the user is only interacting with a graphical proxy of the virtual environment and there is no cross-connection. It’s literally a pixel stream into the browser, and you can’t hack a stream of pixels.
We’ve also created a new concept of an invisible wallet to the cryptocurrency industry. There are 2 types of crypto wallets: the online software wallet, which is losing tens of millions of dollars every day by hacking, and the hardware offline wallet which are offline and so effectively the gold standard for security. We created a new concept of an “Invisible Wallet” using our WebSafe instant, invisible, virtual machines in which we put a wallet. Using a HD Wallet the user can enter their 12-word phrase using the Invisible Keyboard and reconstruct their wallet inside the virtual machine. There’s essentially no attack surface as everything is a graphical proxy. We are adding the MasterKey technology to a cryptocurrency exchange so the exchange no longer needs to hold your private key. This is where MasterKey crosses over from Authentication of users, to Authorization of transactions.
Do you think people are more aware now of the importance of creating a safe cyberspace and protecting their data and users?
Yes. People the world over are being educated by our governments and the media about the growing cyber threat. Businesses and individuals are investing in security. I think it was John Chambers, the head of Cisco, who said: “There are two types of companies in the world, those who have been hacked, and those who don’t know they’ve been hacked”. Everyone is as risk. It’s not personal. This done by software robots. We all use the same technology and are equally vulnerable. Compared to 20 years ago, the internet today is a very dangerous place.
When we pivoted our cloud computing platform technology in this cybersecurity industry in 2015, the total cost of cybercrime globally was 500 billion dollars. This year, one analyst predicts it will be 6 trillion dollars. This is an astronomical number. So, the way we have been doing cybersecurity, which is detect-and-respond, by the numbers is has failed us. The attackers are winning.
This is what we call Cybersecurity 1.0: when you are constantly trying to detect the next creative hack vector using monitoring combined with artificial intelligence, to calibrate a new response. This is always playing catch up and it represents perpetual failure. Cybersecurity 2.0 is the new generation where security is built into the foundations. Leading this today is Passwordless Authentication.
What are the main challenges tech companies will face in the next 5 to 10 years?
As a technology entrepreneur, this is the sort of question I look into every day. Cybersecurity 2.0 will have other technologies designed in from the foundations. I mentioned that we are looking at Transaction Authorization next. This is really big and can be applied to payments, cryptocurrency, healthcare, etc. We are also working on something we call a Transaction Room, which is a bit like a data room but where the user’s endpoint device is not a weak link. We’re able to encode, encrypt and shard data which can then be stored anywhere, but never reconstructed other than back inside an equivalent Transaction Room where each party’s identity is validated and can only be them. I would also like to get back and finish building a new type of Password Manager, like we set out to 2 years ago. This would not expose your credentials to a Man-in-the-Browser, and so would have a formidable technological edge over the current solutions.
But most of this is for next year. Right now, I’m spending my time simply evangelizing the solutions we have available today. How do we communicate with society to let people know these solutions exist now. Any organization with a web portal can implement MasterKey overnight. I think we have a unique advantage over other solutions in that is so accessible to small enterprises. and they make up the bulk of the market (the markets Long Tail).
The BankVault team and I are very proud of the work we’ve done to secure web users, and allow them to take control of their own security.



Leave a comment