$400 million! That’s how much Yahoo’s data breach cost the company upfront: $50 million to compensate users, and the other $350 million was the compromise Yahoo had to make on its acquisition deal with Verizon.
You might think, “Alright, but our people only connect through a VPN.” Think again. Even with cutting-edge security, people are, most often, the ones responsible for leaving the back door open (think weak passwords or phishing).
The Yahoo data breach that compromised 3 billion users happened because an employee clicked on the wrong link.
What’s worse, VPNs can get hacked too. Don’t worry, though—I’ve got your back. I’ll show you exactly what to look for in a VPN and what you should do if your VPN gets hacked.
Looking for a safe VPN you can trust? CyberGhost runs on RAM-only servers and has never been hacked. Download CyberGhost VPN and you’ll never have to worry about VPN data breaches.
How Big VPNs Get Hacked
If your VPN was hacked and you want to know what to do ASAP, you can jump to the Why You Are at Risk If Your VPN Is Hacked.
Before that, let’s look at VPN data breaches. That’ll help you understand VPN weaknesses and learn more about what makes a VPN trustworthy. Let’s check out 3 examples.
1. Pulse Secure VPN Hack
The Pulse Secure VPN hack is the most concerning due to its grave consequences. In early 2021, a security firm audit discovered a vulnerability in Pulse Secure software. Cybercriminals had leveraged this vulnerability entry point to execute malicious code remotely.
The investigation revealed 12 distinct malware families, likely from multiple actors, exploiting the Pulse Secure VPN hack. At least 5 US agencies might have been subject to unauthorized access. That led CISA to issue an emergency directive for all federal agencies to check their file system integrity.

It all comes down to Pulse Secure VPN’s mediocre login process. That’s where I facepalm. The cybercriminals exploited the software’s vulnerable login flow to gain access to legitimate credentials and leverage those to gain higher-level access.
2. Android VPN Hacks (SuperVPN, Gecko VPN, and Chat VPN)
In early 2021, more than 21 million Android users were exposed. Three different free Android VPNs were targeted: SuperVPN, Gecko VPN, and Chat VPN. The cyberattackers harvested deeply sensitive user information and advertised the data cache to the highest bidder on a popular hacker forum.
While I wouldn’t call these services “big VPNs”, they are attracting users in millions since they’re free. If you used these services, the attackers got hold of your data, including email address and password, name, country, device serial number, IDs, IMSI no., type and manufacturer, and payment information.
How did it happen? The attackers admitted they accessed sensitive information because nobody bothered to change the default database credentials. The services were practically begging to be hacked.
That isn’t SuperVPN’s first rodeo, and it likely won’t be its last. In 2020, the service suffered a major data breach that exposed user activity logs, passwords, payment information, and more.
Free VPNs promise cutting-edge digital protection and no activity logs, but the reality is different. If nothing else, this leak effectively confirms that free VPNs:
- Keep sensitive user information
- Couldn’t be further from military-grade protection

Two takeaways: 1) Google, please fix your App Store rating system, and 2) you’re more likely to build a DIY VPN than find a reputable free VPN service.
3. NordVPN Hack
Since paid VPNs work with cybersecurity experts and invest in their infrastructure, they’re less likely to get hacked… right? Usually, that’s the case. Once in a while, though, even trustworthy VPNs experience data breaches.
In March 2018, an unauthorized third party got access to a NordVPN server and its private key, which lets you encrypt and decrypt communications. That meant they could’ve intercepted (and decrypted) any traffic going to the server.
Here’s a neat table summarizing what happened with the Nord VPN hack and what it means.
| Deciphering the NordVPN Hack | |
| What Happened | What It Means |
| Remote unauthorized access to a NordVPN server for 30 days. | Perpetrators could intercept traffic passing through the server for 30 days. |
| Unauthorized third party holds a NordVPN encryption key. The key is valid for 7 months. | Third-party could decrypt information passing through the server.
Third-party could use the key to reroute connections through a different server. The company likely had no idea what was happening, or they would’ve intervened. |
In hindsight, NordVPN could’ve handled the hack better.
An undisclosed remote management system left in place by the data center enabled the NordVPN breach. That shows 1) how difficult it is to ensure the same security level across multiple companies and infrastructures and 2) the importance of choosing a VPN that fully manages its server setup.
These three VPN hacks were essentially caused by lackluster security. Whether it’s weak database protection (free Android VPNs), exploitable user authentication (Pulse Secure), or faulty server setup (NordVPN), one small mistake can easily lead to a major breach.
To understand how VPNs get hacked, we need to know more about VPN encryption and how VPNs work.
What Is VPN Encryption and How Does It Work?
VPNs are complex security solutions with many different types. I’ll discuss the most common type of VPNs (remote access), which act as middlemen between you and the internet.
Remote access VPNs are easy to use and offer high security. Companies like Microsoft, Amazon, and Google rely on them to secure remote workflows. They’re also the kind you get from leading commercial VPN brands, CyberGhost included.
How does the VPN work? You fire up the VPN app, press connect, and your online activity is protected. It may look simple, but, scratch the surface, and you’ll find a lot going on in the backend. VPNs have software and hardware components, and cybercriminals can exploit both.
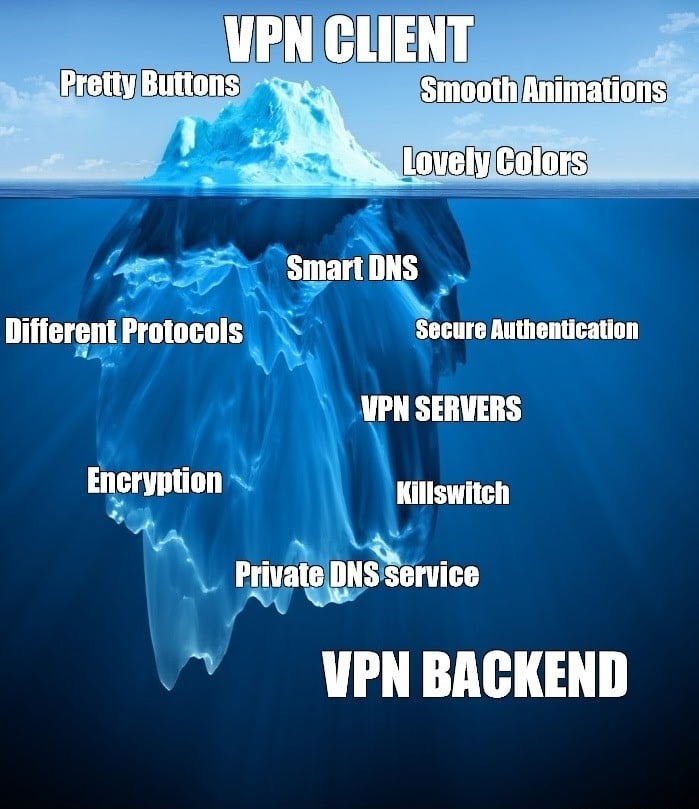
The VPN’s encryption is responsible for encoding your information, ensuring you’re secure and private online.
Here’s how VPN encryption works, step-by-step:
- The VPN uses an encryption key to convert your plain text data (which anyone can read) into cipher text.
- Your data travels over the VPN network as cipher text.
- Using the same key (or, in some cases, a different one), the VPN’s exit node deciphers the information (usually the server you connect to).
- The secure server uses your instructions to interact with the internet on your behalf.
- The VPN exit node encrypts all the information it receives from the website or service you interact with.
- The VPN server sends the cipher text back to you.
- Your VPN uses the encryption key to read the information.
The VPN repeats the process for all your online communications.
Encryption is like a foundation for VPN privacy. While in cipher text, your data can travel over the open internet without anyone understanding it, but the VPN security could have weaknesses.
Let’s check some software and hardware VPN weaknesses.
Common VPN Weaknesses (Software & Hardware)
On the software side, 6 common VPN weaknesses include:
- Poor encryption. Outdated encryption algorithms are vulnerable (may be brute-forced or reverse-engineered). AES-256 bit encryption is the current, military-grade standard for top-secret communication.
- Outdated tunneling protocols. If encryption is your ride, the tunneling protocol is the highway that takes you there. The VPN filters out any information not traveling on the highway. VPNs can use different protocols, with some, like PPTP, being susceptible to password-cracking. That’s why it has become an obsolete authentication method.
WireGuard, IKEv2, IPSec, and OpenVPN are among the safest tunneling protocols.
- Flawed authentication. This is the toll-booth before you get on the highway between your device and the VPN (the tunneling protocol). Instead of paying a fee, you have to pass a serious security check.
Anything weaker than SHA-256 authentication is susceptible to hacking, as PPTP made clear.
- Insecure network management. Secure online communication happens through the VPN servers—the process’s backbone. From the software the VPN runs to local encryption and access rules, improper server management can spell disaster.
- Public DNS. VPNs with their DNS (Domain Name Systems) resolver are better. The DNS is an immense ledger that makes it possible to connect to websites using their name (i.e. duckduckgo[.]com), rather than the IP address (52.250.42.157).
If you don’t use a private DNS, your ISP can see which websites you’ve visited, when, and for how long. With a private DNS, your activity is hidden barring exceptional instances of DNS leaks.
- Data logs. Many VPNs claim to keep zero data logs, but their terms and conditions say something different. VPNs shouldn’t store any sensitive user data. Your IP, bandwidth usage, and especially anything related to your online activity should be protected.
On the hardware side, VPNs can have faulty:
- Data center security. VPN providers should restrict physical access to the VPN servers through multi-factor authentication, including biometric. In some cases, data center breaches may compromise local traffic, and even the network itself.
- Server configuration. The best VPN servers are RAM-only since any hard drive can lead to sensitive data storage. No storage, no problem.
- Location. Laws can force companies to store (and share) sensitive information about you, which is why HQ location is crucial for VPNs. Privacy-friendly jurisdictions include Romania, the British Virgin Islands, Panama, and Switzerland.
Does a VPN prevent cyberattacks? In most instances, yes. Can a VPN be hacked? Of course. One misconfiguration in these areas can lead to a data breach.
Why You Are at Risk If Your VPN Is Hacked
When your VPN is hacked, as a company, you can expect sensitive data leaks, endless security audits, operational disruptions, brand damage, and mounting losses. The fallout can be just as bad for individuals, too.
Here’s what to expect if your VPN is hacked:
Device takeover. If a cybercriminal is targeting you, a hacked VPN can enable them to access and take over your devices using spyware or ransomware.
Leaked credentials. When your VPN security is compromised, anyone eavesdropping on your connection might view your traffic and personal information.
Identity theft. Cybercriminals can use your sensitive data to borrow money, apply for government benefits, take out personal loans, commit credit card fraud, and carry out any other online crimes.
Surveillance. Once exposed by a VPN hack, your ISP, government, and anyone trying to listen in on your connection will be able to see what you’re doing online.
So, how do you deal with a VPN hack? If you’re not up for an uphill battle to convince your bank you were targeted by cybercriminals… you could just declare bankruptcy. Just kidding!
I wouldn’t rush to declare bankruptcy just yet. You can burst out yelling BANKRUPTCY for added dramatic effect and to release stress, but that’s about it.
Here’s what you’ll want to do if your VPN gets hacked.
What to Do If Your VPN Is Hacked
If your VPN ever gets hacked, you should immediately:
- Stop using the VPN. Using a potentially compromised network gives cybercriminals access to your sensitive information.
- Uninstall the VPN. Many VPNs have services running in the background. Depending on the hack, cyberattackers would use it to get more information and even direct access to your devices.
- Ditch the VPN credentials. Assume any data you’ve entered on sign-up got compromised, including your email, password, name, etc. Never use them again. If you use your password for other apps, websites, or emails, change those too. The process is a lot easier if you have a good password manager like the one CyberGhost VPN offers.
- Reassess your VPN. Not every hack is a complete compromise. That said, VPN hacks are more worrisome than others since they handle sensitive information. Be on the lookout for opinions from cybersecurity experts—does the VPN’s response address the issue, was the breach handled professionally?
- Use a better VPN. The safest option is to switch to a more secure VPN, preferably one that hasn’t been hacked, like CyberGhost VPN. When doing so, you can use the Common VPN Weaknesses as a security checklist.
CyberGhost is among the strongest choices if you want a VPN that can’t be hacked. The service doesn’t store any payment information. Whatever data you provide on sign-up remains separate from the network.
CyberGhost VPN has a strict No-Logs policy, and its infrastructure is RAM-only. Hypothetically, if unauthorized third parties got physical access to a CyberGhost VPN server, they’d have to bypass the machine’s local encryption. Unlike other VPNs, CyberGhost VPN experts fully install and manage the software, which minimizes the risk of insecure configurations, as was the case with the NordVPN hack.
If cybercriminals manage to decrypt server communication, they would get… nothing because CyberGhost VPN doesn’t store or link any traffic to you.
Cyberattacks That VPNs Will Protect You From
Assuming they’re not the ones getting hacked, VPNs will protect you from many online threats. Here’s a neat table summarizing what a VPN can and can’t do for you:
| VPNs can protect you from | VPNs can’t protect you from |
| ✔ DDoS Attacks | ❌ Malware or Phishing Attacks |
| ✔ Man-in-the-Middle Attacks | ❌ Backdoor Attacks |
| ✔ Evil Twin Attacks | ❌ Evil Maid Attacks (requires physical access to your computer/device) |
| ✔ Mac Spoofing Attacks | ❌ OS Vulnerabilities (RDP hack, Wi-Fi Sense sharing, etc.) |
| ✔ ARP Spoofing Attacks | ❌ Software Vulnerabilities |
Some VPNs make it easier for cybercriminals to hack you, and we’ve seen how that’s the case with free VPNs.
Other VPNs offer superior protection. The CyberGhost Security Suite for Windows covers more threats than most VPNs, like software and OS vulnerabilities, and malware.
VPNs may not be invulnerable, but they offer great protection from cybercriminals lying in wait. Did you or your company ever get hacked? Was it because someone clicked on the wrong link? Let me know in the comments sections below.
FAQ
It depends on your VPN. The most recent VPN hacks resulted in personal information leaks, exposed user activity logs, and even malware infections. A trustworthy VPN service is less likely to be hacked. When reliable VPNs experience a data breach, the event is usually confined by multiple failovers, like server encryption and virtualization, behavior firewalls, and proactive security management.
CyberGhost VPN, for one, has built its network from the ground up using privacy-by-design principles and a stringent No-Logs policy. On the other hand, free VPNs are gold mines for hackers. Cybercriminals have successfully hacked numerous free Android VPNs and sold highly sensitive user information on the dark web.
It depends on your VPN. Reliable VPN services prevent tracking altogether, even in those countries where ISPs are legally obligated to keep online activity logs. That said, sketchy and free VPN services will make it easier for you to get hacked. Many sell your data to advertisers and various third parties.
If you’re concerned about being tracked, I recommend you rely on a VPN that has optimized its infrastructure for this purpose. CyberGhost VPN’s NoSpy servers are custom-engineered to guarantee the best online protection.
Free VPNs aren’t safe from hacking. Free VPNs have high odds to get hacked, which is even more worrisome considering many of these apps store sensitive user information. CyberGhost VPN has a 45-day money-back guarantee. Take it for a spin and see for yourself why it’s worth every penny.



Leave a comment
Buddy Wynn
Posted on 23/02/2023 at 11:07
If your cell phone, wifi, or pc is already hacked,,
Is the VPN before or after transmission?
Ghostie
Posted on 28/02/2023 at 16:24
Hi, Buddy,
To answer your question, the VPN encrypts your traffic before it leaves your device, regardless of what it is. However, if your hardware is already compromised by malware or a malicious party, no VPN will be able to help with that.
We have a post on how you can tell if your phone is infected and what you can do about it, which you might find helpful.
Stay safe!
Mary Myers
Posted on 18/12/2022 at 07:38
If I get a notification that I don’t know who the sender is, should I NOT hit the link they send about a bank card being misused?
Ghostie
Posted on 20/12/2022 at 10:12
Hi, Mary
Your instinct is correct. If you don’t know who the sender is, you should not, under any circumstance, click on links you receive. There’s a good chance someone might be trying to infect you with malware.
If you have probable cause to believe that your card might be misused, log in to your online bank service (or call customer service) and check the records yourself. And if you see suspicious activity, cancel the card yourself by using a) the online bank portal, b) calling your bank on their official customer service number, or c) by going to the closest office in-person.
Happy Holidays and stay safe!